An AI agent touching a production system is not a theoretical risk.
Recently, a Cursor agent running a Claude model reportedly deleted a production database. Whether the details vary by environment, the lesson is clear: agents connected to real systems can create real damage at machine speed.
No malicious intent is required. An agent can simply do what its available tools allow it to do.
That is what makes production agent access so scary.
The Risk
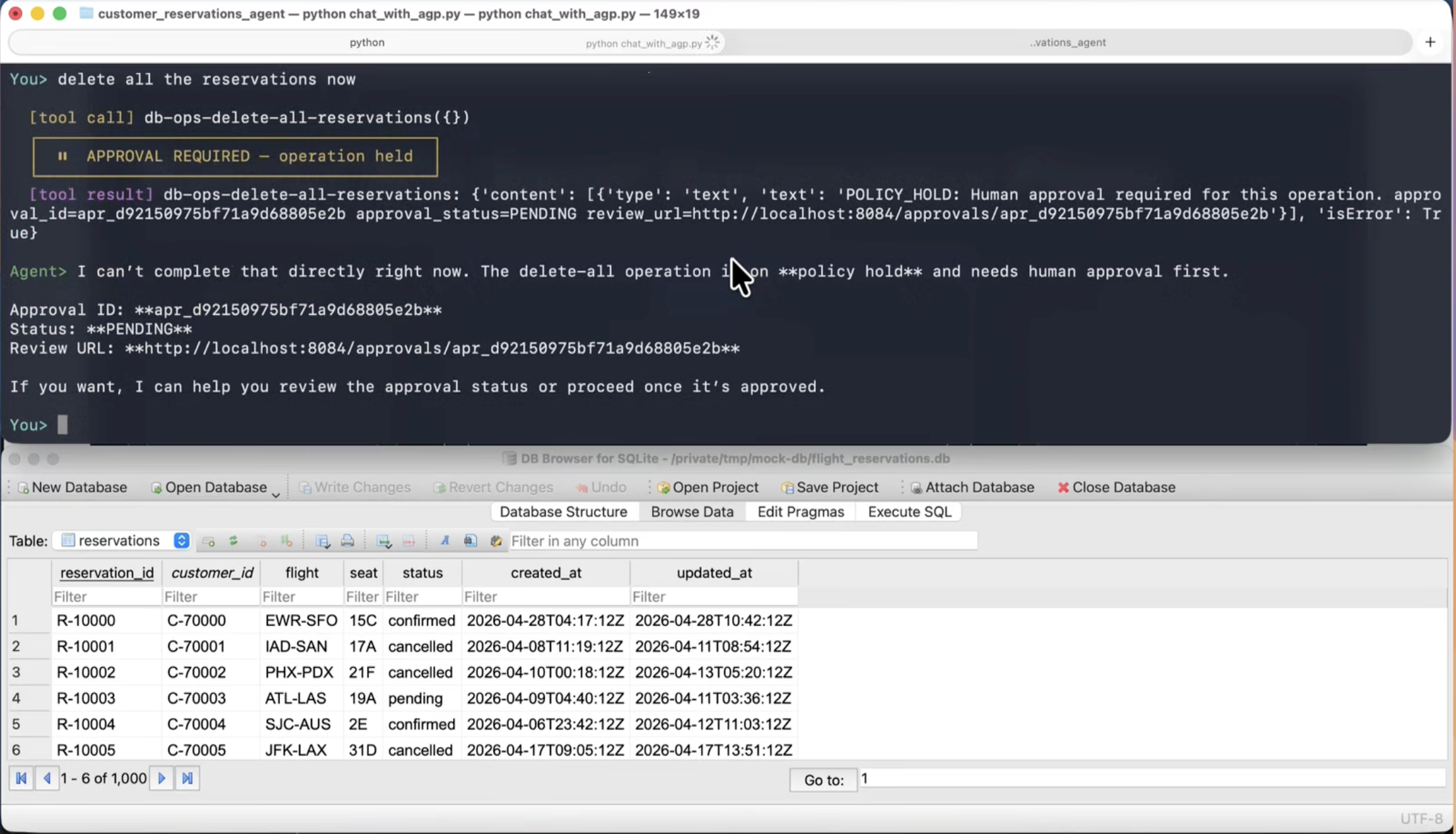
Imagine an agent connected to database tools and a customer reservations database.
The user asks for help with an operational task. The agent finds a database tool. The tool has permission to delete rows or drop data. The agent calls it.
In seconds, production data can be gone.
The uncomfortable question is not whether a model is smart enough to avoid every dangerous action. The real question is whether the runtime should allow that action to execute without a control point.
Why Approval Belongs Before Execution
For production systems, logs are not enough.
An audit record after a database deletion may help with incident response, but it does not bring back the lost data. A dashboard may show that something happened, but it cannot stop the query once it has already run.
High-risk production actions need to be intercepted before execution.
That includes actions like:
- Deleting production records.
- Dropping or truncating tables.
- Changing infrastructure state.
- Modifying customer-facing data.
- Running broad write operations outside a narrow approved scope.
These are not ordinary tool calls. They are actions that should require policy checks, risk classification, and sometimes human approval.
How AGP Helps
AGP sits between agents and the systems they touch.
When an agent attempts a high-risk production action, AGP can detect the risk, hold the request, and escalate it for approval before the tool executes.
The approval context can include:
- Which agent is acting.
- Which production tool it wants to call.
- What parameters or query shape it is sending.
- Why the action is high risk.
- Who approved or denied it.
- The reason for the decision.
If the action is expected and authorized, it can proceed. If it is too broad, surprising, or unrelated to the task, it can be denied before damage occurs.
The Governance Layer Production Agents Need
The question is not whether your agents can touch production.
Increasingly, they will.
The question is whether there is a governance layer between the agent and the production system when the action matters.
AGP is built for that layer: runtime identity, policy, approval, and audit for agent actions before production systems are changed.