Supply-chain compromise often becomes credential compromise.
When a malicious package lands inside a trusted AI or developer runtime, it may not need a sophisticated backend exploit. It can simply look for the credentials already available in that environment.
Those credentials might include:
- API keys.
- Cloud tokens.
- CI secrets.
- Model provider credentials.
- Local authentication material.
Once those credentials leak, the incident can quickly move from one compromised package to broader infrastructure exposure.
The Chain to Break
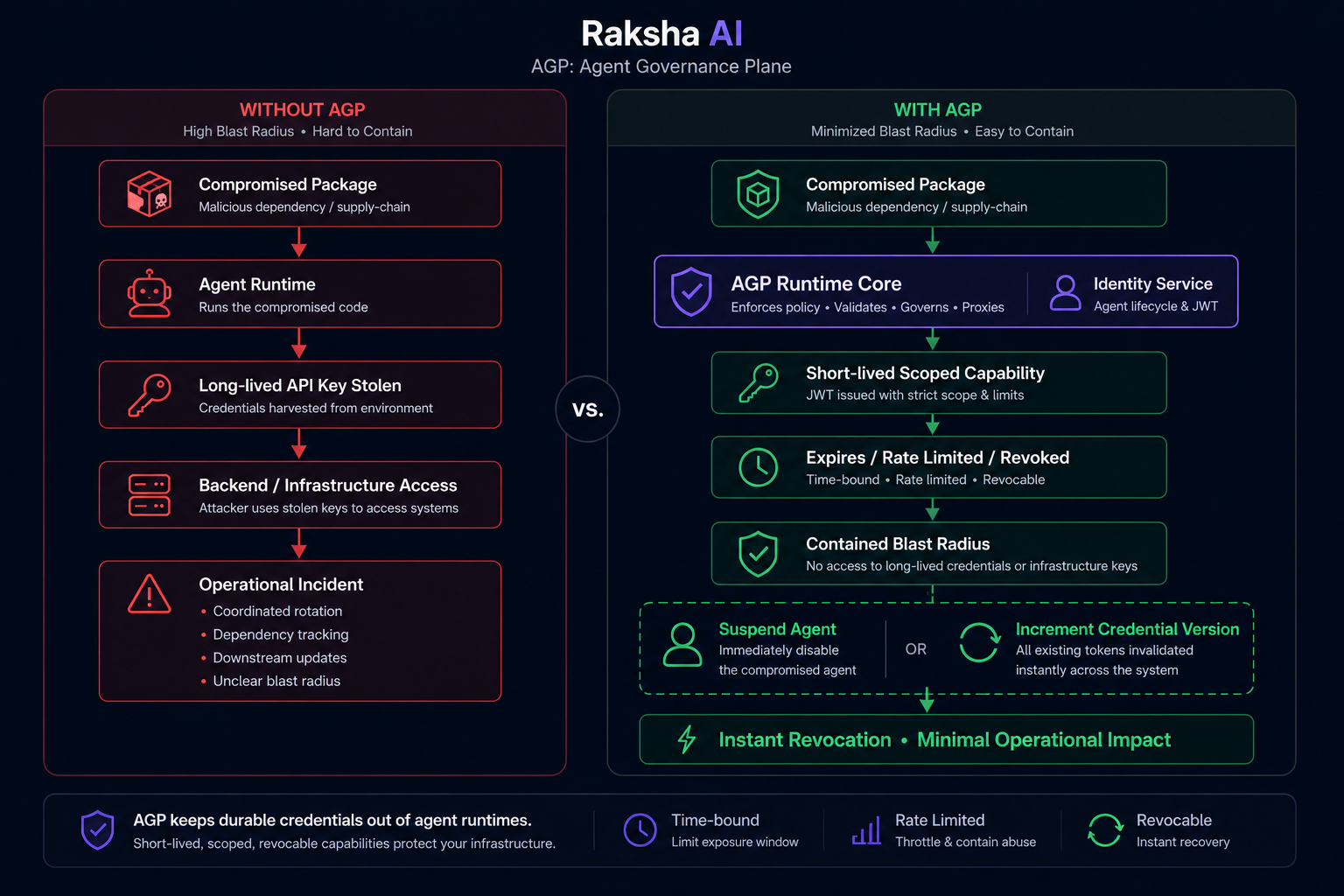
The dangerous chain looks like this:
Supply-chain compromise -> credential compromise -> infrastructure compromiseThe earlier that chain is broken, the smaller the incident becomes.
This matters for agentic systems because agents often sit near powerful tools, model credentials, workflow secrets, and internal APIs. If the agent runtime or one of its dependencies is compromised, long-lived shared credentials can turn a local compromise into a much larger operational problem.
Why Long-Lived Secrets Are Painful
When a backend infrastructure credential leaks, cleanup is rarely simple.
Teams may need to perform dependency graph analysis, coordinate rotation, update downstream services, validate deployments, and manage service disruption risk.
That is a heavy response path.
Revoking an agent capability should not feel like a full infrastructure incident.
How AGP Reduces Blast Radius
AGP is designed to make agent access easier to contain.
Instead of giving agents broad, long-lived backend credentials, AGP can enforce short-lived and scoped capabilities in the runtime path.
That changes the incident response model:
- Agents operate with scoped capabilities.
- Agent and tool access can be rate limited independently.
- A suspicious or compromised agent can be suspended quickly.
- Credential versions can be incremented for fast revocation.
- Tool access can be narrowed without rotating unrelated infrastructure secrets.
The goal is not to pretend supply-chain attacks will never happen.
The goal is to prevent one compromised package from becoming uncontrolled infrastructure access.
Governance as Containment
Agent governance is not only about approvals and audit logs.
It is also about containment.
If a dependency, runtime, or agent process is compromised, AGP gives teams a narrower control surface for revocation, suspension, rate limiting, and blast-radius reduction.
That is the difference between a credential leak that becomes an infrastructure incident and a scoped capability that can be contained.